Bitcoin Miner Botnet images are ready. Bitcoin Miner Botnet are a topic that is being searched for and liked by netizens now. You can Download the Bitcoin Miner Botnet files here. Get all free vectors.
If you’re looking for Bitcoin Miner Botnet pictures information related to the Bitcoin Miner Botnet topic, you have pay a visit to the ideal blog. Our site frequently provides you with suggestions for viewing the maximum quality video and image content, please kindly surf and locate more enlightening video content and images that match your interests.
Bitcoin Miner Botnet. The Ufasoft miner the RCP miner and the Phoenix miner a file with geo-location information for IP address ranges. The Jenkins miner however is a different creature altogether. At Black Hat a pair of researchers demonstrated that its. These are typically more attacks albeit on different servers with a unique domain or IP coordinates.
 A Cryptocurrency Miner Botnet Has Infected More Than Half A Million Machines Hijacking Them To Mine As Much As 3 Bitcoin Blockchain Technology Bitcoin Wallet From pinterest.com
A Cryptocurrency Miner Botnet Has Infected More Than Half A Million Machines Hijacking Them To Mine As Much As 3 Bitcoin Blockchain Technology Bitcoin Wallet From pinterest.com
1 a Monero XMR. Bitcoin mining hardware handles the actual Bitcoin mining process but. Monero has a Jenkins Miner Problem. However it was important to stop it before the attackers compromised more devices. The Jenkins miner however is a different creature altogether. The botnet carries two payloads.
We observed that the botnet performs Bitcoin mining on its victim devices on a growing scale using known mining tools such as xmrig and emech.
By actively spreading Monero mining malware the owner of this botnet has enslaved thousands of computers already. Blogger December 5 2016 at 150 AM. The Smominru miner botnet turns infected machines into miners of the Monero cryptocurrency and is believed to have made its owners around 36m since it started operating in May 2017 – about a. At Black Hat a pair of researchers demonstrated that its. These are typically more attacks albeit on different servers with a unique domain or IP coordinates. If you are a solo miner.
 Source: in.pinterest.com
Source: in.pinterest.com
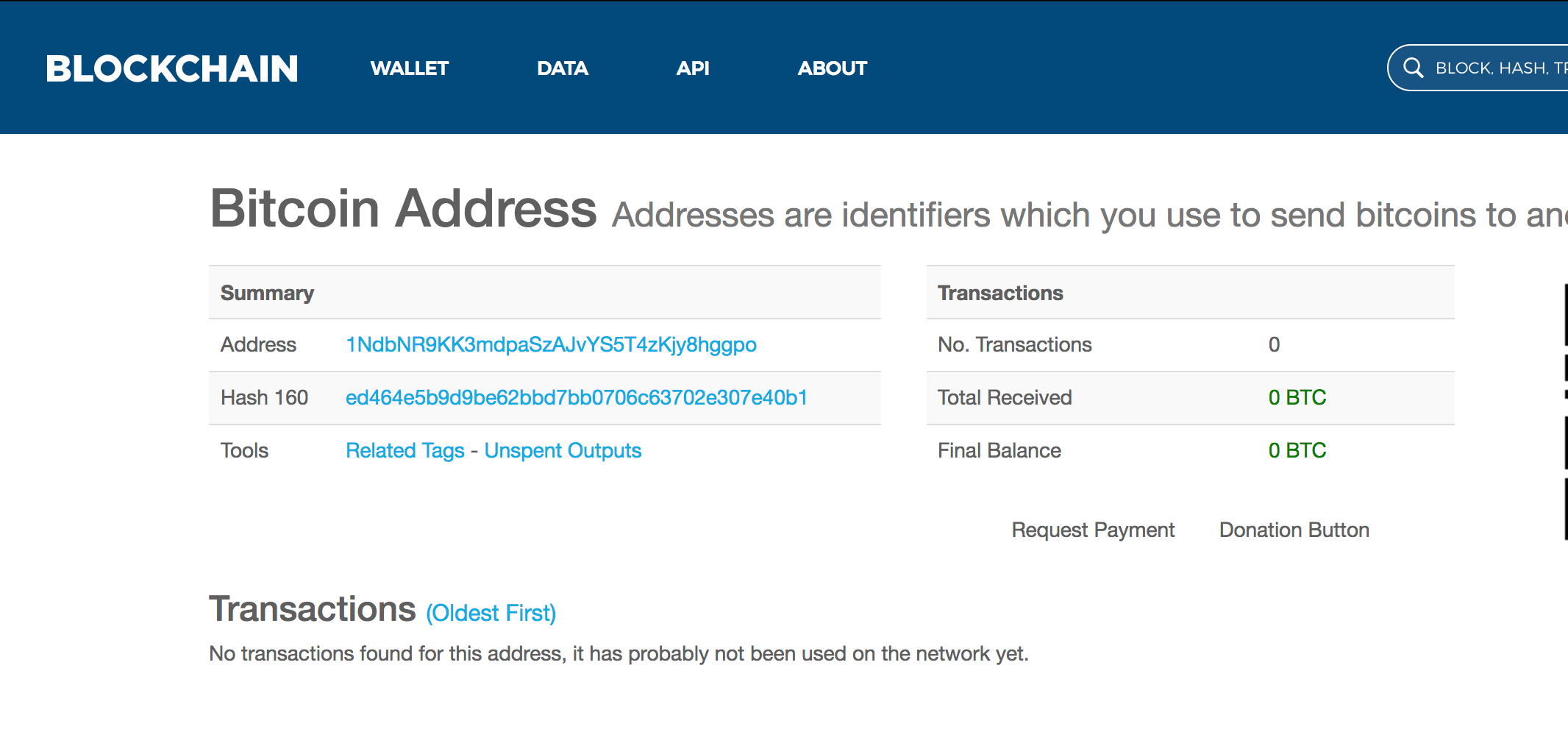
It is suspected this is a Chinese operation designed to mine Monero. Botnet Commands Sent Via Messages Hidden In Bitcoin Blockchain Transactions. The botnet experiment with a Bitcoin-mining module for a week before dropping the module altogether. Bitcoin mining software is equally as important. The Ufasoft miner the RCP miner and the Phoenix miner a file with geo-location information for IP address ranges.
 Source: in.pinterest.com
Source: in.pinterest.com
Did you think about exchanging with the ultimate Bitcoin exchange service - YoBit. It is suspected this is a Chinese operation designed to mine Monero. Creating a Bitcoin-Mining Botnet at No Cost. A network of internet-connected devices that have been compromised by hackers without the knowledge of the legitimate owners. Bitcoins are valuable in large part because mining for bitcoins takes a lot of resources.
 Source: in.pinterest.com
Source: in.pinterest.com
The software will connect you to your mining pool. If you mine with a pool. Security researcher Tolijan Trajanovski analyzed the multi-vector MinerTsunami Botnet that implements SSH lateral movement. As far as I can tell custom-ASIC based Bitcoin mining is continuing to deploy at a fast rate and any profit to be made from Botnet Bitcoin mining is likely to evaporate soon. Posted by Unknown at 1144 AM.
 Source: in.pinterest.com
Source: in.pinterest.com
The software will connect you to your mining pool. We observed that the botnet performs Bitcoin mining on its victim devices on a growing scale using known mining tools such as xmrig and emech. These are typically more attacks albeit on different servers with a unique domain or IP coordinates. The Smominru miner botnet turns infected machines into miners of the Monero cryptocurrency and is believed to have made its owners around 36m since it started operating in May 2017 – about a. Bitcoins are valuable in large part because mining for bitcoins takes a lot of resources.
 Source: pinterest.com
Source: pinterest.com
These are typically more attacks albeit on different servers with a unique domain or IP coordinates. A cryptocurrency miner botnet has infected more than half a million machines hijacking them to mine as much as 36 million worth of monero. Share to Twitter Share to Facebook Share to Pinterest. Next xanthesh verified that the tmp directory was configured to allow the execution of files before checking to see if the miner was already running in memory. The Ufasoft miner the RCP miner and the Phoenix miner a file with geo-location information for IP address ranges.
 Source: pinterest.com
Source: pinterest.com
A fellow security researcher 0xrb shared with me samples of a botnet that propagates using weblogic exploitThe botnet was also discovered by BadPackets 5 days ago and it is still active as of now December 1 2020. A network of internet-connected devices that have been compromised by hackers without the knowledge of the legitimate owners. As far as I can tell custom-ASIC based Bitcoin mining is continuing to deploy at a fast rate and any profit to be made from Botnet Bitcoin mining is likely to evaporate soon. The Smominru miner botnet turns infected machines into miners of the Monero cryptocurrency and is believed to have made its owners around 36m since it started operating in May 2017 – about a. Bitcoin mining hardware handles the actual Bitcoin mining process but.
 Source: pinterest.com
Source: pinterest.com
Monero has a Jenkins Miner Problem. A network of internet-connected devices that have been compromised by hackers without the knowledge of the legitimate owners. BrianKrebs July 19. Did you think about exchanging with the ultimate Bitcoin exchange service - YoBit. Moreover the botnet was still under development when it was uncovered.
 Source: in.pinterest.com
Source: in.pinterest.com
If you mine with a pool. However we leave these aside for now and focus on the botnets architecture instead which is really just a channel for pushing software to infected machines. Blogger December 5 2016 at 150 AM. More specifically it is a completely malicious mining operation. 1 a Monero XMR.
 Source: pinterest.com
Source: pinterest.com
Bitcoin mining hardware handles the actual Bitcoin mining process but. This last resource concealed the miner process name in memory so as to help the botnet evade detection. We observed that the botnet performs Bitcoin mining on its victim devices on a growing scale using known mining tools such as xmrig and emech. The Ufasoft miner the RCP miner and the Phoenix miner a file with geo-location information for IP address ranges. Did you think about exchanging with the ultimate Bitcoin exchange service - YoBit.
 Source: pinterest.com
Source: pinterest.com
The botnet carries two payloads. BrianKrebs July 19. A Botnet is able to control the computers it targets by using. The Ufasoft miner the RCP miner and the Phoenix miner a file with geo-location information for IP address ranges. More specifically it is a completely malicious mining operation.
 Source: in.pinterest.com
Source: in.pinterest.com
Next xanthesh verified that the tmp directory was configured to allow the execution of files before checking to see if the miner was already running in memory. At Black Hat a pair of researchers demonstrated that its. 1 a Monero XMR. However it was important to stop it before the attackers compromised more devices. Moreover the botnet was still under development when it was uncovered.
This site is an open community for users to share their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site beneficial, please support us by sharing this posts to your own social media accounts like Facebook, Instagram and so on or you can also bookmark this blog page with the title Bitcoin Miner Botnet by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.